What is a VPN scam?
A VPN scam entices users with an ad to deceive users, exposing them to security and privacy risks. In some cases, it’s a fake VPN app, and in other cases, it’s a real VPN app that is utilized for malicious purposes to compromise the user’s online security.
A VPN, or virtual private network, lets users send and receive data across public networks as if their devices were directly connected to a private network with an alternate IP address. Most VPN websites are legitimate services used to provide online security and privacy. However, they are also an attractive venue for scammers. Like in many other types of scams, fake VPN and free VPN scams use social engineering to bypass security mechanisms, convince users to deploy malicious code onto their own devices, or compromise their online security in other ways.
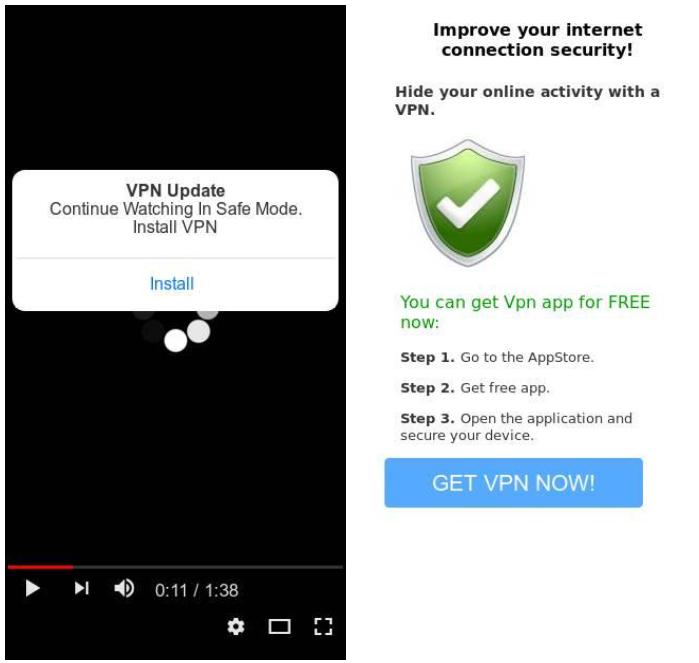
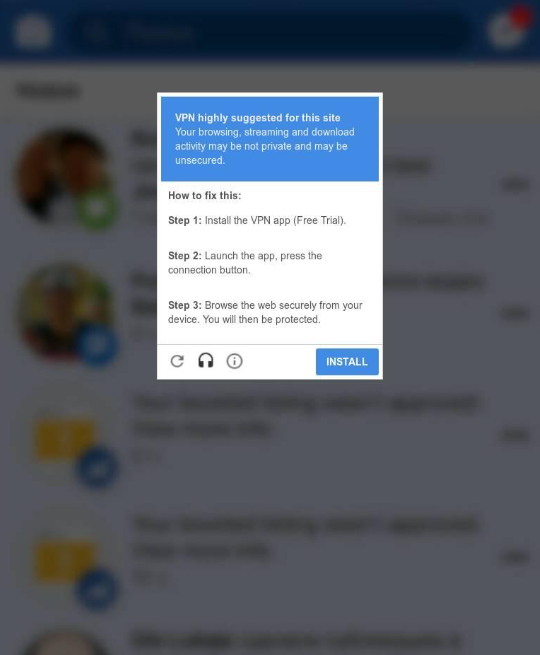
Common VPN ad scams in the start by serving a clickbait ad to the user, in most cases, an image ad disguised to look like a video. They often use content people are likely to want privacy to view—things like porn, pirated sportscasts or movies, or party websites. Once victims click on the ad, they are redirected to a landing page that prompts them to download and install a free VPN app in order to view the content. The app is downloaded directly from the landing page, rather than from the Google Play store, Apple app store, or other third-party websites that have various protectections in place.
Once users have seen these ads, there’s a good chance that they’ll fall victim to the fake VPN apps, especially since there are no fine print or FAQ pages to warn them of the danger, and no contact details of someone they can contact details with questions or concerns. That’s why it’s important for publishers to prevent users from seeing ads for fake VPNs in the first place.
Not all free VPN apps are scams. However, in any situation where VPNs claim they’re free, the VPN provider is making money some other way. Some of the best VPNs like Hola VPN for example, use a freemium model or a legitimate advertising revenue model. However, other free VPNs that have thousands of positive ratings on app stores—Betternet VPN for example—have a high malware presence. And many free VPNs are actually out-and-out scams, which is why a paid VPN provider is often a better bet for security than a free one.
Types of VPN scams
The two primary types of scams are suspicious VPN scams that offer functional free VPNs that compromise the victim’s privacy or security, and fake VPNs that introduce malware into the victim’s device without providing a legitimate service.
Suspicious VPN scams
Suspicious VPN attacks send unsuspecting users to a landing page that prompts them to install a free VPN to view the video they saw in the ad. Unlike fake VPN apps, this VPN software functions like all VPN services and lets the user view videos. But unlike quality VPN providers, suspicious VPNs use the internet traffic they channel to monitor the user’s online activity. The victim may not even be aware that someone has access to their user data and online activities through the free VPN service, or that their security has been compromised.
Fake VPN scams
Unlike suspicious VPNs, fake VPNs and fake VPN apps do not allow users to stream videos. When a user installs a fake VPN, they often introduce malware onto their device instead. Victims are more likely to be aware of the breach to their online security with a fake VPN app, if for no other reason than the fact that they can’t view the video they saw in the ad. Unlike a good VPN, there are no contact details for the VPN services advertised.
Risks of fake VPN scams
The primary risk posed by fake VPNs is to the user’s privacy. In most cases, the scammers want to track the victim’s browsing and search history for targeting purposes.
Ransomware, Trojan horses, and other types of malware are not common in fake VPNs. However, a criminal VPN service can be used to compromise a user’s security and access sensitive data, private data, payment information, banking details, and other user data from online accounts. Criminal VPN providers often track user data and use data-collection tactics that a reputable VPN company would never use, such as DNS leaks and sniffing and keylogging to access private information from the victim’s online activity.
How to detect fake VPN scams?
The best way to spot a fake VPN is to cross-check data points from multiple detection engines, focusing on keywords, images, and domains known to be used in VPN scams.
There are many active community forums in the VPN market that report fake VPNs, share insights on how to spot a fake VPN, and help users find a genuine VPN that maintains their online privacy. But none of those tactics are helpful when a user is served an ad that drives them to a fake VPN app. That’s why the ads need to be detected before victims see them.
Identifying the various clickbait tactics and deceptive elements in social engineering schemes like ads for fake VPNs isn’t easy. It requires sophisticated software and AI that can aggregate and assess data and insights from multiple layers holistically. That includes identifying suspicious language common in a fake VPN service and not likely to be used by a virtual private network with a strong track record—for example, VPNs claiming to offer a free lifetime subscription or other questionable pricing models. But text analysis alone isn’t enough. The text needs to be cross-referencd with the image used in the ad, and the domain the landing page uses to assess whether the domain is similar to ones used in past scams. If those patterns are seen, it’s a good indication that the add is fraudulent.
How to block fake VPN scams?
The best way to block fake VPN apps is to block ads that lead to them.

The vast majority of scams rely on free VPN app ads shown on websites owned by third parties, especially ones that have a high volume of internet traffic. However, given the frequency of the attacks, it can be very challenging for the owners of those websites to tackle the problem on their own. Since each user is served a different ad, from a different source, ad ops teams can’t recreate the bad VPN experience. Therefore, the only solution is to detect the ads before they’re served, block them, and show alternative ads instead.
GeoEdge makes it easy to do exactly that. By integrating a piece of code in a publisher’s website, we can monitor ads before they’re displayed, make sure that they were sent by a legitimate advertiser, and that the ad meets the publisher’s brand standards. If we detect ads for fake VPNs, we can block them and exchange them with a legitimate ad in real time. Not only that, we update the ad exchange that sent the ad for fake VPNs so it can update its exclusion list.